Perkoon vs UndercoverGPT
Side-by-side comparison to help you choose the right product.
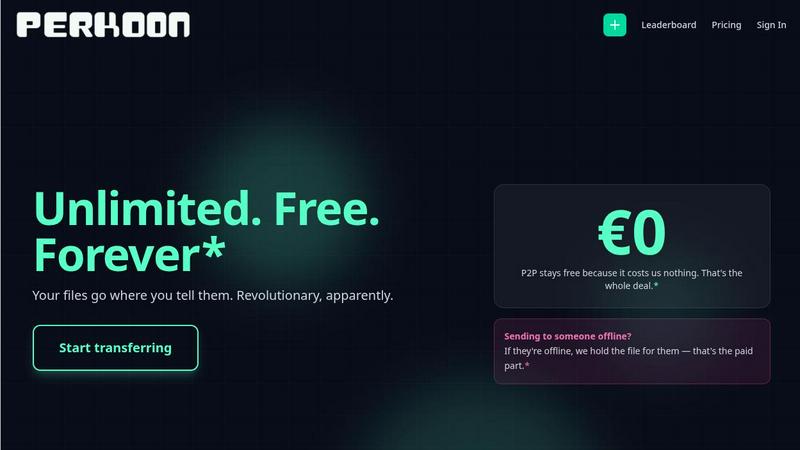
Perkoon sends unlimited files directly between browsers for free with no signup.
Last updated: March 4, 2026

UndercoverGPT
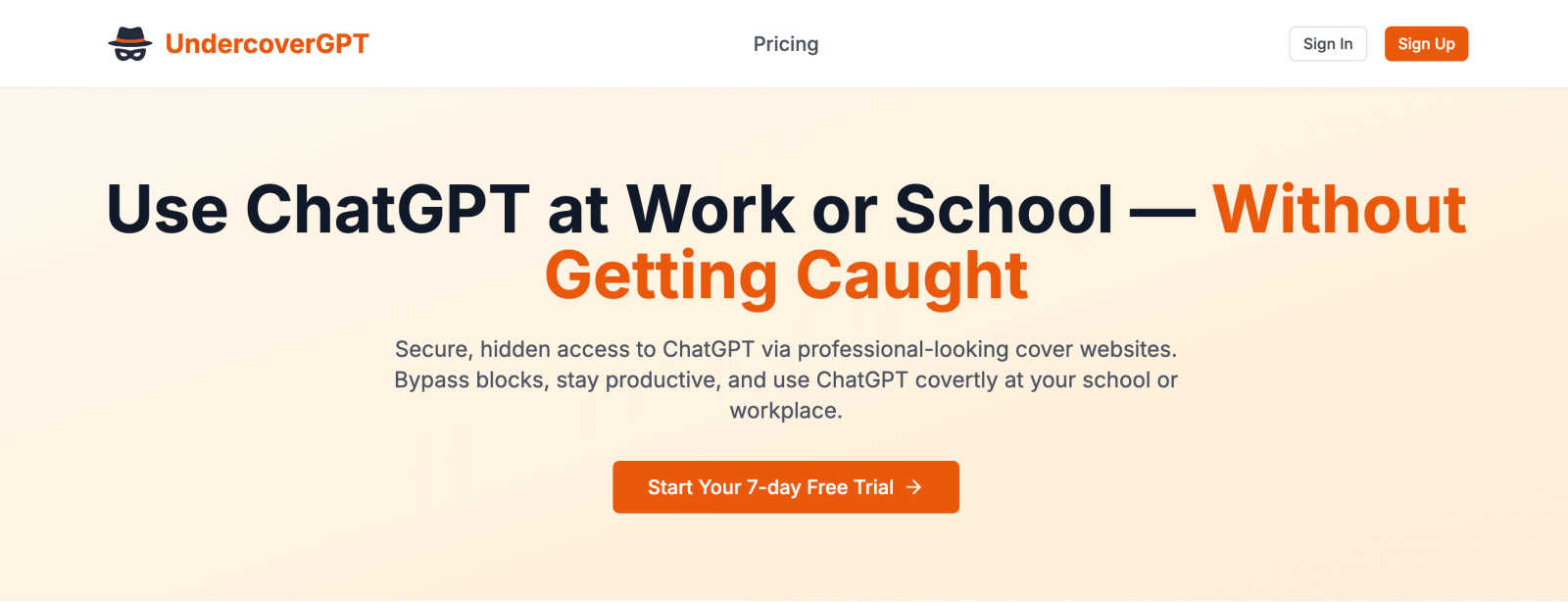
Access ChatGPT at work using professional cover sites to bypass blocks.
Last updated: March 1, 2026
Visual Comparison
Perkoon
UndercoverGPT
Feature Comparison
Perkoon
Unlimited Free P2P Transfer
This is the core of Perkoon. When both sender and recipient are online, files stream directly from one browser to another using peer-to-peer technology. This means there are absolutely no file size limits, no mandatory sign-ups, and because the data bypasses central servers entirely, it's private by design and costs Perkoon nothing to operate. It's free for you, forever, with no hidden catches.
Encrypted Cloud Storage for Offline Sends
Need to send a file to someone who isn't online right now? Perkoon's cloud storage feature has you covered. Files are securely encrypted on Perkoon's servers and held until the recipient is ready to download. This is the service's paid feature, and the pricing is transparently structured to honestly cover the cost of running and maintaining this infrastructure—no profit markup on privacy.
Native AI & Automation Integration
Perkoon is built for the age of automation. Instead of forcing AI agents to awkwardly scrape web pages, Perkoon provides a native JavaScript object (window.__perkoon) and a Command Line Interface (CLI) tool. This allows scripts, bots, and AI assistants to interact with the file transfer service directly and programmatically, enabling seamless automated workflows without friction.
Transparent Referral & Rewards Program
Perkoon incentivizes growth in a mutually beneficial way. Share your unique referral link; when someone signs up through it, you both get a bonus boost of cloud storage. When they complete 1GB of P2P transfers, you both earn even more. The program includes chain rewards, meaning you can earn bonuses from your referrals' referrals, building a network that continuously rewards active users.
UndercoverGPT
Professional Cover Websites
UndercoverGPT operates through a rotating selection of meticulously designed, professional-looking websites that mimic common corporate and academic tools. These facades, such as fake analytics dashboards, project management boards, or internal wikis, are visually convincing and generate no suspicious network traffic. This allows you to run AI queries in plain sight, with the interface fully masking the underlying ChatGPT session, ensuring your activities blend seamlessly into your standard work environment.
Stealth Network Bypass
The tool employs advanced techniques to bypass common network filters and firewall blocks that institutions use to restrict access to ChatGPT and similar platforms. It doesn't just use a simple proxy; it routes your connection through its cover sites in a way that appears as normal web browsing to network administrators. This sophisticated bypass mechanism ensures reliable, uninterrupted access to AI capabilities without triggering security alerts or access denials.
Full ChatGPT Functionality
Despite operating undercover, you retain access to the complete, unadulterated suite of ChatGPT features. This includes the latest model capabilities for text generation, complex analysis, code writing and debugging, creative tasks, and detailed research assistance. There is no feature downgrade or limited version—you get the full power of AI to draft, edit, brainstorm, and solve problems at maximum speed and efficiency, all within the secure shell of the cover site.
Privacy-Focused Design
UndercoverGPT is built with discretion as a core principle. Your queries and interactions are handled with a focus on privacy, minimizing data footprints on your local device and within the network. The service is designed to leave no obvious traces of AI tool usage in your browser history or local cache in its standard form, helping you maintain a low profile and protect your productivity strategy in sensitive environments.
Use Cases
Perkoon
Sending Large Project Files to Clients
Freelancers, designers, and videographers can instantly send massive project files—think 50GB video edits or design suites—directly to a client's browser. No compressing, splitting, or begging clients to sign up for a service. It's a frictionless, professional transfer that respects both parties' time and data.
Automated Backup & Data Pipeline Scripts
Developers and sysadmins can integrate Perkoon's CLI into their scripts. Automate the transfer of log files, database dumps, or backup archives from a server to a designated recipient or storage node. The native API access means reliable, programmatic file movement without building custom infrastructure.
Privacy-Conscious Document Sharing
Lawyers, journalists, or anyone handling sensitive information can share documents with the assurance of true P2P privacy. Since files in a direct transfer never pass through a third-party server, there's zero risk of corporate scanning, data mining, or unauthorized access by the service provider itself.
AI Agent File Management
An AI assistant managing your workflow can use Perkoon's built-in window.__perkoon object to send you generated reports, receive documents for processing, or distribute outputs to a team. This turns Perkoon into a seamless file highway for autonomous agents, supercharging productivity without manual intervention.
UndercoverGPT
The Corporate Professional
Employees in large corporations with strict SaaS approval policies can use UndercoverGPT to bypass internal blocks. It enables them to quickly draft client communications, generate reports, analyze data, and prepare presentations using AI, all while their screen displays a benign-looking "internal performance dashboard" or "compliance checklist," maintaining full productivity without conflict with IT protocols.
The University Student
Students at universities that block ChatGPT on campus networks can leverage UndercoverGPT for essential academic support. They can get help with essay structuring, research summarization, coding assignments, and studying, accessing AI through what appears to be a "digital library portal" or "research citation tool," ensuring they have the same academic advantages as peers with unrestricted access.
The Remote Contractor
Freelancers and contractors working on client systems or through monitored virtual private networks (VPNs) can use UndercoverGPT to maintain their AI-powered workflow. It allows them to generate content, debug code, or translate documents efficiently without requesting special permissions or raising red flags with the client's IT department, ensuring project delivery speed and professionalism.
The Research Analyst
Analysts in sensitive or competitive fields who cannot use public AI tools due to data policy concerns can utilize the covert operation of UndercoverGPT. They can use it behind a "data visualization platform" facade to brainstorm hypotheses, structure complex findings, and polish research language without ever visibly connecting to an external AI service, protecting their methodological secrecy.
Overview
About Perkoon
Perkoon is the file transfer service that cuts through the corporate nonsense to deliver what you actually need: a fast, private, and refreshingly honest way to move your data. Built for real people tired of artificial limits, mandatory accounts, and services that monetize their privacy, Perkoon gets back to basics with two powerful modes. Its flagship offering is unlimited, free P2P transfer that beams files directly between browsers with no size caps and no middleman—your data never touches Perkoon's servers, ensuring true privacy and keeping the service free forever. For sending to offline recipients, Perkoon offers encrypted cloud storage as a straightforward paid feature, transparently covering the real cost of servers. Uniquely designed for the modern workflow, Perkoon is built for both humans and AI, featuring native automation tools and a CLI so machines can interact directly without clunky workarounds. It's the no-BS, efficiency-first solution for anyone who just wants their files to go from point A to point B without the hassle, hidden fees, or privacy violations.
About UndercoverGPT
UndercoverGPT is the definitive stealth engine for unlocking AI productivity in locked-down digital environments. It is designed for students and professionals who face network blocks, stringent IT policies, or institutional bans on AI tools like ChatGPT. This innovative solution provides secure, hidden access to the full power of advanced AI through a sophisticated suite of professional-looking cover websites. The core mission is seamless, covert operation: you interact with ChatGPT's complete functionality, but it is entirely concealed behind convincing, mundane facades such as corporate analytics dashboards, project management portals, or academic research libraries. This tool is essential for anyone who needs to accelerate their workflow—drafting critical emails, writing comprehensive reports, debugging code, or conducting deep research—but is prevented from doing so directly at their school, university, or workplace. UndercoverGPT prioritizes discretion and operational efficiency above all, ensuring you can leverage cutting-edge AI to maintain peak performance and a competitive edge, all while appearing to use ordinary, approved web applications. It transforms restricted access into a strategic advantage.
Frequently Asked Questions
Perkoon FAQ
Is the P2P transfer really free forever?
Yes, absolutely. The peer-to-peer transfer technology sends files directly between browsers. This process costs Perkoon essentially nothing in server bandwidth or storage overhead. Therefore, they can offer it as a free service indefinitely, with no file size limits. The business model is sustained by the optional paid cloud storage feature.
What happens if the recipient is offline?
If the recipient is not online to receive a direct P2P transfer, Perkoon will seamlessly offer to use its encrypted cloud storage instead. This is a paid feature. The file is uploaded, encrypted on Perkoon's servers, and a link is generated. The recipient can then download the file at their convenience, with the link expiring after a set period.
Can Perkoon see what I'm sending in a P2P transfer?
No. In a direct P2P transfer, the file data streams exclusively between the two users' browsers using WebRTC technology. Perkoon's servers only facilitate the initial connection ("signaling") but never handle the actual file data. They are technically incapable of seeing, scanning, or storing the content of your transfer.
Which browsers are supported?
For the full, unlimited P2P experience, Chromium-based browsers like Chrome, Edge, and Brave work perfectly. Firefox and Safari have inherent browser restrictions that can limit transfer speeds or maximum file sizes for P2P connections. All major browsers support the cloud storage send and download functionality.
UndercoverGPT FAQ
How does UndercoverGPT avoid detection?
UndercoverGPT avoids detection by routing all AI interactions through its network of professional cover websites. These sites are designed to look and behave like ordinary corporate or academic web tools, generating standard web traffic that does not match the patterns of known AI platforms. This method effectively bypasses keyword and URL-based filters, making your activity appear as routine browsing.
Is it legal to use UndercoverGPT?
UndercoverGPT is a software tool, and its legality depends on your local laws and the terms of service of the network you are using. It is your responsibility to ensure compliance with institutional policies (workplace, school) and applicable regulations. The tool is designed for productivity in restricted environments, but users must assess their specific situation regarding authorized tool usage.
Do I need technical skills to set it up?
No, UndercoverGPT is designed for immediate, hassle-free use. There is typically no complex setup or configuration required. You access the service through a web browser, select a cover site facade, and begin using the integrated ChatGPT interface. It's built for agility, allowing anyone to start leveraging covert AI power within seconds, regardless of technical expertise.
Does it work on all restricted networks?
While UndercoverGPT employs advanced bypass techniques designed to work on most common institutional firewalls and network filters (like those in schools and corporations), no tool can guarantee 100% success on every possible network configuration. Its methods are continuously updated to counteract widespread blocking techniques, offering a highly reliable solution for the vast majority of restricted environments.
Alternatives
Perkoon Alternatives
Perkoon is a straightforward, privacy-focused file transfer service in the productivity and management category. It cuts through the clutter by offering unlimited peer-to-peer transfers without signups, a model that prioritizes user control and data privacy. Users often seek alternatives for various reasons. Some need different pricing structures or specific features like advanced collaboration tools. Others may require broader platform compatibility or simply prefer a service with a more traditional cloud-first approach over Perkoon's peer-to-peer core. When evaluating options, consider your primary needs. Key factors include transfer methods, privacy guarantees, cost structure, and ease of use. Determine if you value direct device-to-device transfers or always-available cloud storage, and whether automation capabilities or sheer simplicity are your top priority.
UndercoverGPT Alternatives
UndercoverGPT is a specialized AI assistant tool designed for productivity in restricted environments. It operates within the category of stealth productivity software, providing covert access to ChatGPT through professional cover sites to bypass network blocks at work or school. Users often explore alternatives for various reasons, including budget constraints, a need for different feature sets like mobile access or integration capabilities, or simply a preference for a more straightforward access method without the stealth layer. The specific platform requirements of their IT environment can also drive the search. When evaluating other options, key considerations should include the tool's core method of access, its reliability in evading detection, the overall user experience for getting tasks done quickly, and the value provided relative to its cost. The right fit balances discretion with seamless functionality.