Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right product.

Deeploy
Deeploy empowers organizations to govern AI systems with real-time oversight, ensuring compliance and reducing risk.
Last updated: March 1, 2026
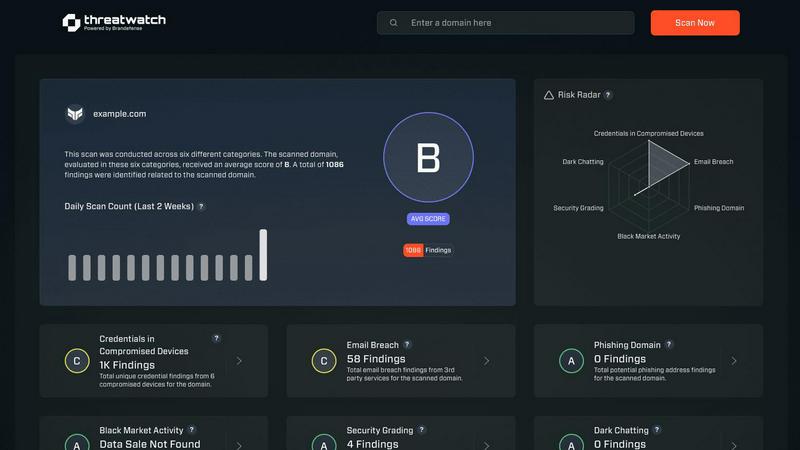
Threat Watch
Instantly assess your cybersecurity health and get actionable insights on critical threats.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Deeploy offers complete visibility across your AI landscape, enabling organizations to discover, onboard, and manage every AI system from a single interface. This eliminates blind spots, allowing seamless integration with existing MLOps or GenAI platforms without the hassle of migration.
Control Frameworks
With Deeploy, navigating AI regulations becomes straightforward. The platform provides guided workflows to help you stay compliant, whether you choose from default control frameworks like ISO 42001 or NIST AI RMF, or build your own custom frameworks tailored to your needs.
Control Implementation
Deeploy's governance framework translates into enforceable controls that engineers can easily follow. By providing clear, actionable requirements and automating evidence collection, organizations can accelerate compliance by up to 90%, freeing teams from tedious manual tasks.
Real-Time Monitoring
Stay ahead of potential issues with Deeploy's real-time monitoring capabilities. The platform alerts users instantly about model drift or performance drops, ensuring that AI systems are performing optimally while maintaining compliance. This proactive approach helps prevent incidents before they impact users.
Threat Watch
Real-Time Cyber Health Dashboard
Gain an instant, visual snapshot of your organization's security posture. This dynamic dashboard aggregates data across all monitored categories, presenting a clear, prioritized score. Watch your cyber health metrics update in real-time as new threats are detected or existing ones are mitigated, enabling lightning-fast strategic decisions without manual data crunching.
Automated Exposure & Vulnerability Scanning
Continuously and automatically scan your digital assets for weaknesses. The platform proactively identifies unpatched software, misconfigured systems, and network vulnerabilities that could serve as entry points for attackers. This hands-off, always-on surveillance ensures no critical gap goes unnoticed, freeing your team to focus on remediation.
Dark Web & Credential Monitoring
Actively patrol the dark web and other illicit sources for your organization's compromised data. Threat Watch alerts you immediately if employee credentials, corporate emails, or sensitive information appear in breached databases or for sale, allowing you to enforce password resets and contain account takeover attempts before damage occurs.
Phishing Attack Surface Analysis
Identify and secure your most vulnerable phishing targets. The platform analyzes which corporate email addresses are exposed and being targeted in phishing campaigns. This intelligence allows you to tailor employee security training, strengthen email filters, and proactively block malicious domains targeting your specific organization.
Use Cases
Deeploy
Streamlining AI Governance
Organizations can leverage Deeploy to centralize all AI initiatives, transforming a chaotic environment into a well-structured governance framework. This allows for consistent monitoring and compliance with regulations, making scaling AI initiatives much simpler.
Enhancing Compliance Processes
With Deeploy's guided workflows, teams can easily navigate complex AI regulations. This is particularly useful for compliance officers who need to ensure that all AI systems adhere to legal standards, thereby minimizing the risk of penalties.
Improving AI Performance
Deeploy's real-time monitoring feature helps organizations identify performance issues before they escalate. This is essential for maintaining user trust and ensuring that AI systems deliver accurate and reliable results without compliance risks.
Accelerating AI Deployment
By reducing the deployment time of AI models from days or weeks to just an hour, Deeploy empowers organizations to iterate quickly and efficiently. This agility ensures that non-technical teams can also engage with AI systems, enhancing transparency and collaboration across the board.
Threat Watch
Proactive Risk Management for IT Teams
IT departments use Threat Watch to shift from a reactive fire-fighting model to a proactive security stance. By receiving automated, prioritized alerts on vulnerabilities and exposures, teams can efficiently allocate resources to patch the most critical issues first, dramatically reducing the organization's overall attack surface and improving operational efficiency.
Executive & Board-Level Reporting
Security leaders leverage the platform's clear, concise dashboards to communicate cyber risk in business terms to executives and the board. The visual health score and trend data provide undeniable evidence of the security program's ROI and current posture, facilitating informed decisions on budget and strategy with compelling, real-time data.
Rapid Incident Response Triage
When a potential breach is suspected, responders use Threat Watch to rapidly investigate. They can instantly check if specific credentials were leaked, if related domains are phishing targets, or if corporate assets appear on the dark web. This accelerates the investigation, containment, and eradication phases of incident response.
Compliance Audit Preparation
Organizations facing compliance frameworks like SOC 2, ISO 27001, or GDPR use Threat Watch to maintain continuous control monitoring. The platform provides documented evidence of ongoing vulnerability assessment, dark web monitoring, and exposure management, simplifying audit processes and demonstrating due diligence in protecting sensitive data.
Overview
About Deeploy
Deeploy is your ultimate solution for AI governance infrastructure, specifically tailored for organizations looking to scale their artificial intelligence initiatives responsibly and effectively. It transforms the chaotic and often risky landscape of AI into a streamlined, compliant, and trusted ecosystem. Designed for technical teams, compliance officers, and business leaders alike, Deeploy centralizes oversight, compliance, and monitoring of every AI system in your organization—from traditional machine learning models to advanced generative AI applications. The platform empowers users to automate governance workflows, achieve real-time visibility, and ensure adherence to crucial standards like the EU AI Act. With Deeploy, organizations can shift from a fragmented array of unmonitored AI initiatives to a cohesive, auditable, and fully governed AI environment, significantly minimizing risks and accelerating time-to-value. This comprehensive governance layer allows teams to innovate rapidly while maintaining control, ensuring that AI can be an asset rather than a liability.
About Threat Watch
Threat Watch is the definitive cybersecurity command center for modern businesses. In today's accelerated digital environment, threats evolve at breakneck speed. This platform delivers the rapid, actionable intelligence you need to keep pace. It operates by continuously analyzing your organization's entire digital footprint—from assets and network vulnerabilities to critical exposures—to generate a real-time, comprehensive overview of your cyber health. Designed for IT professionals and security teams across companies of all sizes, Threat Watch cuts through the noise. It automates complex assessments and prioritizes risks, enabling you to move from insight to action in minutes, not days. Its core value is simple: proactive resilience. By swiftly uncovering compromised credentials, breached accounts, phishing vectors, and dark web exposures, Threat Watch empowers you to neutralize risks before they escalate into costly breaches. It's not just monitoring; it's your strategic advantage for staying ahead in the cybersecurity race.
Frequently Asked Questions
Deeploy FAQ
What types of organizations can benefit from Deeploy?
Deeploy is designed for any organization that relies on AI, including those in sectors like finance, healthcare, manufacturing, and technology. Its governance infrastructure meets the needs of technical teams, compliance officers, and business leaders.
How does Deeploy ensure compliance with AI regulations?
Deeploy simplifies compliance through guided workflows that align your AI systems with established frameworks like ISO 42001 and NIST AI RMF. This ensures that organizations can meet regulatory standards without excessive complexity.
Can Deeploy integrate with existing AI systems?
Yes, Deeploy seamlessly connects with various MLOps and GenAI platforms, allowing you to discover, onboard, and manage your AI landscape without migration pains, ensuring a smooth integration process.
How does real-time monitoring work in Deeploy?
Deeploy's real-time monitoring feature provides instant alerts for any performance issues, such as model drift or anomalies, enabling organizations to address potential risks proactively. This ensures that AI systems operate effectively and remain compliant.
Threat Watch FAQ
How quickly can I see results with Threat Watch?
Immediately. Once you initiate your scan by providing the relevant domain or asset information, Threat Watch begins analyzing data from its live threat intelligence feeds. You will receive an initial cyber health assessment and exposure report within minutes, giving you actionable insights from the moment you log in.
What types of assets does Threat Watch monitor?
Threat Watch is designed to monitor your digital footprint. This primarily includes your public-facing IT infrastructure such as domain names, IP addresses, and associated network blocks. It also focuses on your human assets by scanning for exposed employee credentials, email addresses, and their presence in data breaches and phishing kits.
Is Threat Watch suitable for a small business without a dedicated security team?
Absolutely. Threat Watch is built for businesses of all sizes. Its user-friendly interface and automated prioritization are perfect for small business owners or general IT providers who need enterprise-grade security insights without requiring deep expertise. It tells you exactly what needs attention first, making efficient use of limited time and resources.
How does the platform prioritize the risks it finds?
Threat Watch uses a risk-based algorithm that considers factors like the severity of the vulnerability, the criticality of the exposed asset, and the active exploitation of the threat in the wild. It doesn't just list problems—it scores and ranks them, so you know precisely which issues pose the most immediate danger to your organization and should be addressed first.
Alternatives
Deeploy Alternatives
Deeploy is a cutting-edge AI governance infrastructure designed specifically for organizations looking to scale their artificial intelligence initiatives. By transforming disparate AI systems into a centralized and compliant framework, Deeploy enables businesses to manage their AI assets effectively and responsibly. Users often seek alternatives to Deeploy for various reasons, including pricing considerations, specific feature requirements, or unique platform integration needs tailored to their operational environment. When selecting an alternative, it's crucial to evaluate the core functionalities and compatibility with existing systems. Look for solutions that offer robust compliance management, real-time visibility, and seamless onboarding capabilities, ensuring that your organization can maintain a high level of oversight while accelerating its AI ambitions.
Threat Watch Alternatives
Threat Watch is a dynamic business intelligence platform that provides instant cybersecurity health assessments. It delivers actionable insights on compromised accounts and devices, helping organizations identify and prioritize risks before they escalate. Users often explore alternatives to find a solution that aligns perfectly with their budget, specific feature requirements, or existing technology stack. Needs vary widely, from deeper integration capabilities to different pricing models or more specialized reporting functions. When evaluating other options, prioritize tools that offer real-time, actionable intelligence, automated risk assessments, and comprehensive monitoring. The right platform should deliver clear visibility into your security posture with efficiency, enabling your team to act swiftly against threats.
