Karolium vs Threat Watch
Side-by-side comparison to help you choose the right product.
Karolium is a zero-code platform that rapidly customizes intelligent business solutions for seamless digital.
Last updated: February 28, 2026
Threat Watch
Instantly assess your cybersecurity health and get actionable insights on critical threats.
Last updated: March 1, 2026
Visual Comparison
Karolium

Threat Watch
Feature Comparison
Karolium
Unified Zero-Code Development
Karolium’s zero-code development environment allows users to create and customize applications without writing a single line of code. This feature empowers users to design tailored solutions at unprecedented speeds, facilitating rapid deployment and adaptation to changing business needs.
Predictive and Prescriptive Analytics
Built-in analytics capabilities provide organizations with insights that forecast trends and recommend optimal actions. This feature enables data-driven decision-making, allowing businesses to stay ahead of market changes and improve operational efficiency.
Seamless Integration
Karolium enables effortless integration with both legacy systems and modern microservices applications. This feature ensures organizations can augment their existing application ecosystems without the need for extensive redevelopment, maximizing their software investments.
Continuous Updates and Enhancements
With an active SaaS subscription model, Karolium guarantees users access to the latest technological advancements and regular updates. This commitment to continuous improvement helps businesses stay relevant and competitive in an ever-evolving digital landscape.
Threat Watch
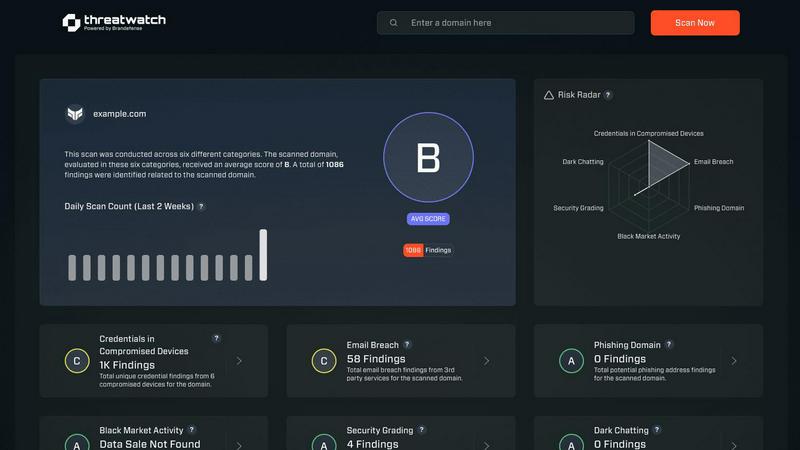
Real-Time Cyber Health Dashboard
Gain an instant, visual snapshot of your organization's security posture. This dynamic dashboard aggregates data across all monitored categories, presenting a clear, prioritized score. Watch your cyber health metrics update in real-time as new threats are detected or existing ones are mitigated, enabling lightning-fast strategic decisions without manual data crunching.
Automated Exposure & Vulnerability Scanning
Continuously and automatically scan your digital assets for weaknesses. The platform proactively identifies unpatched software, misconfigured systems, and network vulnerabilities that could serve as entry points for attackers. This hands-off, always-on surveillance ensures no critical gap goes unnoticed, freeing your team to focus on remediation.
Dark Web & Credential Monitoring
Actively patrol the dark web and other illicit sources for your organization's compromised data. Threat Watch alerts you immediately if employee credentials, corporate emails, or sensitive information appear in breached databases or for sale, allowing you to enforce password resets and contain account takeover attempts before damage occurs.
Phishing Attack Surface Analysis
Identify and secure your most vulnerable phishing targets. The platform analyzes which corporate email addresses are exposed and being targeted in phishing campaigns. This intelligence allows you to tailor employee security training, strengthen email filters, and proactively block malicious domains targeting your specific organization.
Use Cases
Karolium
Rapid Application Development
Businesses can utilize Karolium to quickly develop custom applications that cater to specific workflows, reducing the time and resources typically required for traditional coding. This agility allows for faster market response and innovation.
Enhanced Decision-Making
Organizations can leverage Karolium's predictive and prescriptive analytics to enhance decision-making processes. By utilizing data insights, companies can make informed choices that drive strategic growth and operational efficiency.
Intelligent Supply Chain Management
Karolium's platform supports intelligent applications that optimize supply chain operations. From demand forecasting to warehousing management, businesses can streamline processes while ensuring real-time collaboration across all levels.
AI-Driven Business Solutions
Karolium empowers enterprises to integrate AI capabilities within their applications seamlessly. This allows organizations to harness AI for various purposes, such as automation, predictive analysis, and improved customer interactions, driving measurable outcomes.
Threat Watch
Proactive Risk Management for IT Teams
IT departments use Threat Watch to shift from a reactive fire-fighting model to a proactive security stance. By receiving automated, prioritized alerts on vulnerabilities and exposures, teams can efficiently allocate resources to patch the most critical issues first, dramatically reducing the organization's overall attack surface and improving operational efficiency.
Executive & Board-Level Reporting
Security leaders leverage the platform's clear, concise dashboards to communicate cyber risk in business terms to executives and the board. The visual health score and trend data provide undeniable evidence of the security program's ROI and current posture, facilitating informed decisions on budget and strategy with compelling, real-time data.
Rapid Incident Response Triage
When a potential breach is suspected, responders use Threat Watch to rapidly investigate. They can instantly check if specific credentials were leaked, if related domains are phishing targets, or if corporate assets appear on the dark web. This accelerates the investigation, containment, and eradication phases of incident response.
Compliance Audit Preparation
Organizations facing compliance frameworks like SOC 2, ISO 27001, or GDPR use Threat Watch to maintain continuous control monitoring. The platform provides documented evidence of ongoing vulnerability assessment, dark web monitoring, and exposure management, simplifying audit processes and demonstrating due diligence in protecting sensitive data.
Overview
About Karolium
Karolium is a revolutionary unified zero-code platform meticulously crafted to redefine how businesses develop and deploy applications. With its cutting-edge capabilities, it merges iPaaS, aPaaS, oPaaS, and AIPaaS into a singular solution that accelerates digital transformation. Organizations can leverage ready-to-deploy modules to create codeless applications that are seamlessly aligned with their unique business needs. The platform stands out as a premier enterprise intelligence solution, equipped with built-in predictive and prescriptive analytics that empower organizations to make informed, data-driven decisions. Designed for enterprises looking to boost operational efficiency, Karolium simplifies AI integration into existing systems, facilitating smooth transitions and rapid customization without the usual complexities associated with coding. With an active SaaS subscription model, users continuously benefit from the latest innovations, ensuring they maintain a competitive edge in today's fast-paced digital landscape.
About Threat Watch
Threat Watch is the definitive cybersecurity command center for modern businesses. In today's accelerated digital environment, threats evolve at breakneck speed. This platform delivers the rapid, actionable intelligence you need to keep pace. It operates by continuously analyzing your organization's entire digital footprint—from assets and network vulnerabilities to critical exposures—to generate a real-time, comprehensive overview of your cyber health. Designed for IT professionals and security teams across companies of all sizes, Threat Watch cuts through the noise. It automates complex assessments and prioritizes risks, enabling you to move from insight to action in minutes, not days. Its core value is simple: proactive resilience. By swiftly uncovering compromised credentials, breached accounts, phishing vectors, and dark web exposures, Threat Watch empowers you to neutralize risks before they escalate into costly breaches. It's not just monitoring; it's your strategic advantage for staying ahead in the cybersecurity race.
Frequently Asked Questions
Karolium FAQ
What is Karolium?
Karolium is a unified zero-code platform designed for businesses to develop and deploy applications rapidly and efficiently. It combines various capabilities to facilitate digital transformation and enhance operational efficiency.
Who can benefit from using Karolium?
Karolium is ideal for enterprises seeking to improve their application development processes, integrate AI solutions, and enhance decision-making capabilities without the complexities of traditional coding.
How does Karolium simplify AI integration?
Karolium provides a code-free environment that allows organizations to create AI-driven applications seamlessly. This integration ensures that AI capabilities are accessible and can be incorporated into existing workflows effortlessly.
What kind of support does Karolium offer?
Karolium operates under an active SaaS subscription model, providing users with continuous access to the latest features, updates, and technological advancements, ensuring that they always have the tools they need to succeed.
Threat Watch FAQ
How quickly can I see results with Threat Watch?
Immediately. Once you initiate your scan by providing the relevant domain or asset information, Threat Watch begins analyzing data from its live threat intelligence feeds. You will receive an initial cyber health assessment and exposure report within minutes, giving you actionable insights from the moment you log in.
What types of assets does Threat Watch monitor?
Threat Watch is designed to monitor your digital footprint. This primarily includes your public-facing IT infrastructure such as domain names, IP addresses, and associated network blocks. It also focuses on your human assets by scanning for exposed employee credentials, email addresses, and their presence in data breaches and phishing kits.
Is Threat Watch suitable for a small business without a dedicated security team?
Absolutely. Threat Watch is built for businesses of all sizes. Its user-friendly interface and automated prioritization are perfect for small business owners or general IT providers who need enterprise-grade security insights without requiring deep expertise. It tells you exactly what needs attention first, making efficient use of limited time and resources.
How does the platform prioritize the risks it finds?
Threat Watch uses a risk-based algorithm that considers factors like the severity of the vulnerability, the criticality of the exposed asset, and the active exploitation of the threat in the wild. It doesn't just list problems—it scores and ranks them, so you know precisely which issues pose the most immediate danger to your organization and should be addressed first.
Alternatives
Karolium Alternatives
Karolium is a state-of-the-art zero-code platform tailored for rapid customization of enterprise solutions, facilitating seamless digital transformation. It falls under the development category, specifically focusing on empowering businesses to create and deploy applications without traditional coding. Users often seek alternatives to Karolium due to factors like pricing concerns, feature sets that may not fully align with their specific needs, or the desire for different integrations that better suit their existing ecosystems. When exploring alternatives, it’s crucial to assess the platform’s capabilities in zero-code customization, its analytics features, and the ease of integration with current systems. Additionally, consider the update frequency, customer support, and overall user experience to ensure the chosen solution meets both immediate and long-term business objectives.
Threat Watch Alternatives
Threat Watch is a dynamic business intelligence platform that provides instant cybersecurity health assessments. It delivers actionable insights on compromised accounts and devices, helping organizations identify and prioritize risks before they escalate. Users often explore alternatives to find a solution that aligns perfectly with their budget, specific feature requirements, or existing technology stack. Needs vary widely, from deeper integration capabilities to different pricing models or more specialized reporting functions. When evaluating other options, prioritize tools that offer real-time, actionable intelligence, automated risk assessments, and comprehensive monitoring. The right platform should deliver clear visibility into your security posture with efficiency, enabling your team to act swiftly against threats.