Threat Watch vs Zignt
Side-by-side comparison to help you choose the right product.
Threat Watch
Instantly assess your cybersecurity health and get actionable insights on critical threats.
Last updated: March 1, 2026
Zignt automates contract signing with secure, reusable templates to save you time.
Last updated: March 1, 2026
Visual Comparison
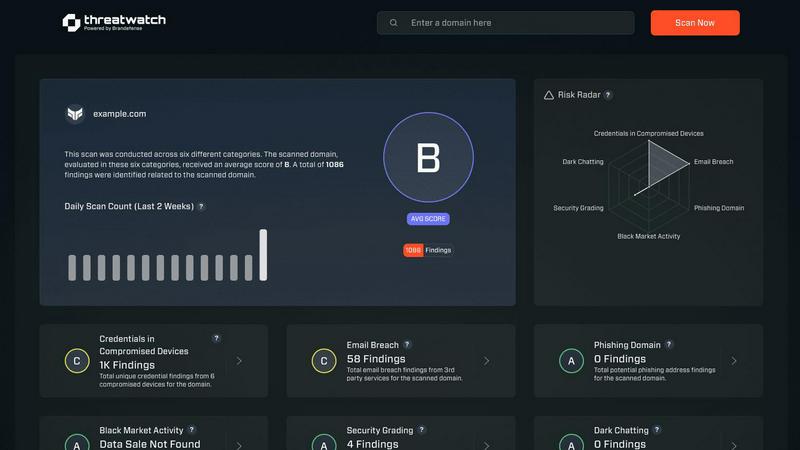
Threat Watch
Zignt

Feature Comparison
Threat Watch
Real-Time Cyber Health Dashboard
Gain an instant, visual snapshot of your organization's security posture. This dynamic dashboard aggregates data across all monitored categories, presenting a clear, prioritized score. Watch your cyber health metrics update in real-time as new threats are detected or existing ones are mitigated, enabling lightning-fast strategic decisions without manual data crunching.
Automated Exposure & Vulnerability Scanning
Continuously and automatically scan your digital assets for weaknesses. The platform proactively identifies unpatched software, misconfigured systems, and network vulnerabilities that could serve as entry points for attackers. This hands-off, always-on surveillance ensures no critical gap goes unnoticed, freeing your team to focus on remediation.
Dark Web & Credential Monitoring
Actively patrol the dark web and other illicit sources for your organization's compromised data. Threat Watch alerts you immediately if employee credentials, corporate emails, or sensitive information appear in breached databases or for sale, allowing you to enforce password resets and contain account takeover attempts before damage occurs.
Phishing Attack Surface Analysis
Identify and secure your most vulnerable phishing targets. The platform analyzes which corporate email addresses are exposed and being targeted in phishing campaigns. This intelligence allows you to tailor employee security training, strengthen email filters, and proactively block malicious domains targeting your specific organization.
Zignt
Unlimited Signature Templates
Build your contract template once and leverage it forever without any recurring cost. Using a simple drag-and-drop editor, you can add signature blocks, date fields, and text boxes to any PDF in minutes. This "configure once, use unlimited times" model is the cornerstone of Zignt, designed to save you hours on every single contract and completely eliminate the frustration of recreating standard documents.
AI-Powered Renewal Management
Never miss a critical deadline again. Zignt's AI automatically scans your executed contracts to detect and track key dates like renewals and expirations. It then provides a centralized dashboard view of all upcoming milestones and sends smart, customizable reminders before deadlines approach. This transforms contract management from a reactive, manual hunt into a proactive, automated system.
Seamless Sharing & Signer Options
Accelerate the signing process with flexible delivery methods. Send contracts directly via email with automated reminder sequences, or generate a secure, shareable Zignt Link for instant access. You can optionally require ID verification for signers and offer multiple signing formats, including typed or drawn signatures, to reduce friction and get documents executed faster.
Enterprise-Grade Security & Compliance
Execute contracts with absolute confidence. Every signature through Zignt is legally binding and compliant with major global standards like the E-SIGN Act, UETA, and eIDAS. The platform employs 256-bit SSL/TLS encryption, is GDPR ready, and maintains a comprehensive, court-admissible audit trail that records every action, timestamp, and IP address for full legal defensibility.
Use Cases
Threat Watch
Proactive Risk Management for IT Teams
IT departments use Threat Watch to shift from a reactive fire-fighting model to a proactive security stance. By receiving automated, prioritized alerts on vulnerabilities and exposures, teams can efficiently allocate resources to patch the most critical issues first, dramatically reducing the organization's overall attack surface and improving operational efficiency.
Executive & Board-Level Reporting
Security leaders leverage the platform's clear, concise dashboards to communicate cyber risk in business terms to executives and the board. The visual health score and trend data provide undeniable evidence of the security program's ROI and current posture, facilitating informed decisions on budget and strategy with compelling, real-time data.
Rapid Incident Response Triage
When a potential breach is suspected, responders use Threat Watch to rapidly investigate. They can instantly check if specific credentials were leaked, if related domains are phishing targets, or if corporate assets appear on the dark web. This accelerates the investigation, containment, and eradication phases of incident response.
Compliance Audit Preparation
Organizations facing compliance frameworks like SOC 2, ISO 27001, or GDPR use Threat Watch to maintain continuous control monitoring. The platform provides documented evidence of ongoing vulnerability assessment, dark web monitoring, and exposure management, simplifying audit processes and demonstrating due diligence in protecting sensitive data.
Zignt
Accelerating Sales Agreements
Sales teams can close deals at the speed of conversation. By pre-building proposal and service agreement templates, reps can generate, send, and get contracts signed within minutes of a verbal agreement. Real-time tracking and automated reminders keep the process moving, drastically shortening sales cycles and improving the customer experience without any per-signature costs.
Streamlining HR Onboarding
Human Resources departments can automate the entire new hire paperwork process. Create templates for offer letters, NDAs, and policy acknowledgments, then send them in batches to multiple new hires simultaneously. The secure, mobile-friendly signing process allows candidates to complete documentation from any device, accelerating start dates and reducing administrative backlog.
Managing Vendor & Client Contracts
Operations and legal teams gain total control over external agreements. Use Zignt to standardize vendor SOWs, client master service agreements, and partnership contracts. The AI renewal tracker ensures you never auto-renew an unfavorable contract by mistake, while the centralized repository and audit trail provide instant visibility into all active obligations.
Facilitating Freelancer & Contractor Work
For businesses that frequently engage independent contractors, Zignt simplifies engagement. Quickly send standardized work agreements and statements of work. The platform's link-sharing feature is perfect for one-off projects, allowing freelancers to sign instantly without account creation, getting projects started faster and ensuring legal protection for both parties.
Overview
About Threat Watch
Threat Watch is the definitive cybersecurity command center for modern businesses. In today's accelerated digital environment, threats evolve at breakneck speed. This platform delivers the rapid, actionable intelligence you need to keep pace. It operates by continuously analyzing your organization's entire digital footprint—from assets and network vulnerabilities to critical exposures—to generate a real-time, comprehensive overview of your cyber health. Designed for IT professionals and security teams across companies of all sizes, Threat Watch cuts through the noise. It automates complex assessments and prioritizes risks, enabling you to move from insight to action in minutes, not days. Its core value is simple: proactive resilience. By swiftly uncovering compromised credentials, breached accounts, phishing vectors, and dark web exposures, Threat Watch empowers you to neutralize risks before they escalate into costly breaches. It's not just monitoring; it's your strategic advantage for staying ahead in the cybersecurity race.
About Zignt
Zignt is the high-velocity contract management platform engineered to eliminate friction from your document workflow. Built for modern businesses that demand speed without sacrificing security, Zignt transforms the slow, costly, and manual process of creating, sending, and signing contracts into a seamless, automated operation. Its core value proposition is powerful yet simple: create a contract template once and send it for signature an unlimited number of times, completely eliminating per-signature fees that plague other platforms. Designed for teams of all sizes, from fast-growing startups to established enterprises, Zignt empowers legal, sales, HR, and operations teams to move faster. With an intuitive drag-and-drop builder, batch sending capabilities, and real-time tracking, it cuts down contract cycle times from days to minutes. Every action is fortified with bank-grade security and compliant with global e-signature laws, ensuring your agreements are not only fast but also legally ironclad. Zignt is the essential tool for businesses looking to accelerate deal closure, improve operational visibility, and reclaim countless hours lost to administrative overhead.
Frequently Asked Questions
Threat Watch FAQ
How quickly can I see results with Threat Watch?
Immediately. Once you initiate your scan by providing the relevant domain or asset information, Threat Watch begins analyzing data from its live threat intelligence feeds. You will receive an initial cyber health assessment and exposure report within minutes, giving you actionable insights from the moment you log in.
What types of assets does Threat Watch monitor?
Threat Watch is designed to monitor your digital footprint. This primarily includes your public-facing IT infrastructure such as domain names, IP addresses, and associated network blocks. It also focuses on your human assets by scanning for exposed employee credentials, email addresses, and their presence in data breaches and phishing kits.
Is Threat Watch suitable for a small business without a dedicated security team?
Absolutely. Threat Watch is built for businesses of all sizes. Its user-friendly interface and automated prioritization are perfect for small business owners or general IT providers who need enterprise-grade security insights without requiring deep expertise. It tells you exactly what needs attention first, making efficient use of limited time and resources.
How does the platform prioritize the risks it finds?
Threat Watch uses a risk-based algorithm that considers factors like the severity of the vulnerability, the criticality of the exposed asset, and the active exploitation of the threat in the wild. It doesn't just list problems—it scores and ranks them, so you know precisely which issues pose the most immediate danger to your organization and should be addressed first.
Zignt FAQ
Are Zignt signatures legally binding?
Absolutely. Zignt signatures are fully compliant with key electronic signature laws worldwide, including the E-SIGN Act in the US, UETA, and the eIDAS regulation in the EU. Every signed document includes a detailed audit trail with timestamps, IP addresses, and email verification, making it court-admissible and legally enforceable.
How does the unlimited template model work?
You pay nothing per signature. Instead, you create a reusable template for a specific contract type (e.g., Sales Agreement). Once built, you can send that template to be signed an unlimited number of times to different recipients. This model is designed for volume, saving significant costs compared to platforms that charge for every single signature event.
What security measures does Zignt have?
Zignt employs bank-grade 256-bit SSL/TLS encryption for all data in transit and at rest. The platform adheres to stringent international standards, including GDPR for data privacy. It maintains SOC 2 compliance and provides a complete, tamper-evident audit trail for every document, ensuring military-level security for your sensitive contracts.
Can my team collaborate on contracts?
Yes, Zignt includes robust team management features. You can invite unlimited team members and set granular permissions to control who can create templates, send contracts, or only view documents. This enables seamless collaboration across departments like sales, legal, and operations while maintaining security and oversight over the entire contract lifecycle.
Alternatives
Threat Watch Alternatives
Threat Watch is a dynamic business intelligence platform that provides instant cybersecurity health assessments. It delivers actionable insights on compromised accounts and devices, helping organizations identify and prioritize risks before they escalate. Users often explore alternatives to find a solution that aligns perfectly with their budget, specific feature requirements, or existing technology stack. Needs vary widely, from deeper integration capabilities to different pricing models or more specialized reporting functions. When evaluating other options, prioritize tools that offer real-time, actionable intelligence, automated risk assessments, and comprehensive monitoring. The right platform should deliver clear visibility into your security posture with efficiency, enabling your team to act swiftly against threats.
Zignt Alternatives
Zignt is a dynamic contract management platform in the business intelligence category, designed to automate workflows from template creation to secure, instant signing. It streamlines operations with AI-powered tracking and reusable templates to boost team productivity and legal compliance. Businesses often explore alternatives to find a better fit for their specific needs. This could be driven by budget constraints, the need for different feature sets like advanced integrations, or requirements for a different user experience scale. The search for the right tool is a strategic step toward optimal operational efficiency. When evaluating other solutions, prioritize core functionality that matches your workflow. Key considerations should include the flexibility of template creation, the robustness of security and audit trails, the transparency of pricing models, and the overall ease of use for your entire team. The goal is to secure a platform that becomes a seamless extension of your business process.
